Machine Learning, a useful tool for hardware cybersecurity
What will this article cover?
- Why Hardware cybersecurity is important
- Which kind of attacks apply to hardware security devices
- An overview of the capabilities of Machine Learning
- How Machine Learning can improve current hardware cybersecurity attacks
- How Applus+ Laboratories’ hacking expertise helps to identify and prevent cybersecurity vulnerabilities
Author: Victor Micó, Security Evaluator and Machine Learning Advisor at Applus+ Laboratories
What is hardware cybersecurity?
Many devices rely on hardware cybersecurity in order to give us protection. These devices compute complex cryptographic algorithms in order to encrypt the information they handle. For this reason, there are different methods of attacking these kinds of devices.
Hardware cybersecurity attack methods
In the context of hardware cybersecurity, there are two kinds of attack methods:
- Active attacks consist of disturbing a device while it is conducting sensitive operations. This is commonly known as Fault Injection. There are multiple ways of injecting faults: optical, voltage, or electromagnetic. Changing the normal flow of operations allows security checks to be bypassed and sensitive information to be obtained.
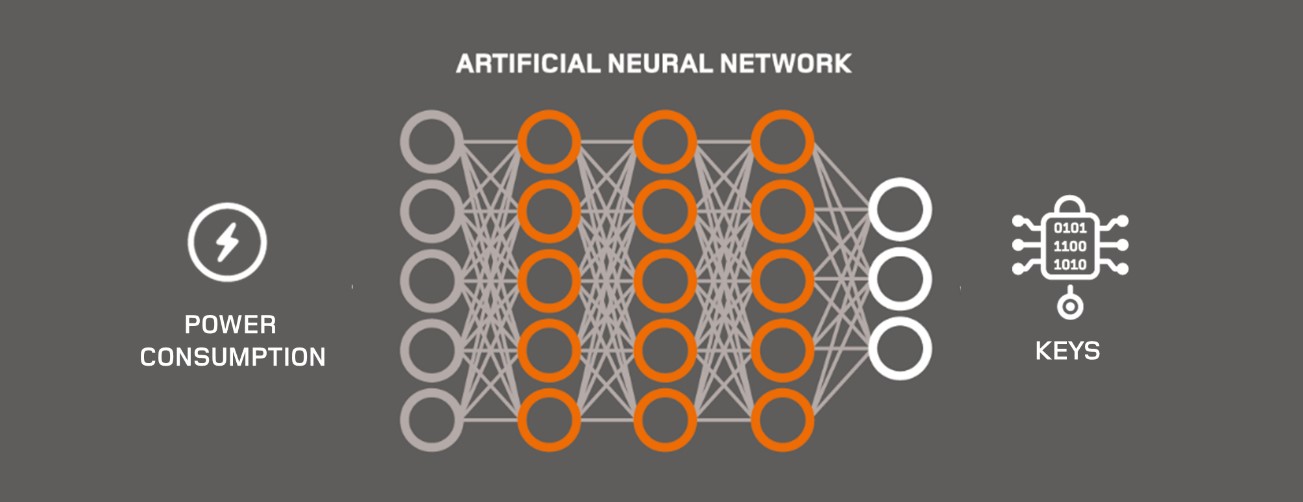
- Passive attacks involve observing or measuring the device without interfering with their normal operation. There are multiple ways of measuring a device while conducting secure operations: power consumption, electromagnetic emanation, timing, or even heat or sound. Each of these constitutes a side channel source. By analyzing the information contained in these sources, it is possible to obtain sensitive information that is supposed to stay confidential, such as encryption keys.
Side Channel attacks aim to retrieve keys by attacking the implementation of the cryptographic algorithms. On the one hand, in order to be protected against these attacks, developers have to apply multiple countermeasures. The countermeasures aim to reduce the leakage by adding noise to the signal, masking the intermediate operations, or by adding fake operations.
On the other hand, the attackers need to collect traces, identify the attack points, conduct statistical analyses to identify the leakage and the PoI (Points of Interest), and finally, conduct the side channel attacks.
With the help of Machine Learning (ML) techniques, it is possible to bypass, or reduce, the effect of these countermeasures, making it necessary to strengthen the security of chips and other IT products.
An overview of Machine Learning
In recent years, ML has become useful for a large number of tasks, from classifying images, to translating text, and even self-driving cars, to cite some sound examples.
Typically, it is typically necessary to have a huge amount of relevant data in order to make an ML model produce valuable results. Then, using statistical techniques and algorithms, the model is tuned to make it learn iteratively about the data presented.
How are Machine learning techniques helping to exploit Hardware cybersecurity attacks?
Machine Learning techniques can be applied to Side Channel and Fault Injection in order to facilitate, improve and speed up obtaining successful results in these kinds of attacks. In particular, ML helps Side Channel and Fault injection by:
- Automatic selection of features: ML models do not require an accurate selection of the PoI (Points of Interest) in order to be successful.
- Less need to preprocess the signal:
- Alignment: it is possible to train a CNN (Convolutional Neural Network) with misaligned traces.
- Filter: there is no need to filter the signal to improve the SNR before analyzing; the neural network internally conducts the necessary filtering in order to classify the traces.
- The ability to bypass classical Side Channel countermeasures:
- Masking: the neural networks are capable of combining information from more than one temporal location, allowing high order attacks, and thus, bypassing the masking countermeasures.
- Shuffling: it is possible to train a neural network to retrieve multiple target points, and thus, bypass the shuffling countermeasure.
- Random delays: the CNN networks are able to extract the information even if the temporal location is shifted.
- Automatic selection of Fault Injection parameters: ML can be used to automate the Fault Injection parameters, and therefore, reduce the time needed to conduct a Fault Injection attack.
ML techniques facilitate and open new attack paths; therefore, it is necessary to consider these threats.
Applus+ Laboratories, hacking expertise to identify and prevent cybersecurity vulnerabilities
Applus+ IT laboratories supports chip and hardware manufacturers evaluating the security of their products against state-of-the-art attack techniques, including Side Channel and Fault Injection attacks sourced by ML. Our experts support vendors from the very conception of the product, through product testing and security assessments.